The crypto industry has framed its quantum reckoning as a single catastrophic “Q-Day” moment when a sufficiently powerful machine arrives, old cryptographic keys shatter, and blockchain history unravels. This week, that moment may have been brought forward into this decade.
The Ethereum Foundation’s Mar. 24 post-quantum (PQ) roadmap shows that the realistic quantum threat to Ethereum centers on forged signatures enabling theft and impersonation, and that selecting stronger cryptographic algorithms is the comparatively manageable layer of the problem.
The coordination infrastructure underneath it is an order of magnitude harder.
EF’s FAQ ranks the exposed surfaces in a specific order: user accounts (externally owned accounts, or EOAs), high-value operational keys at exchanges, bridges, custody hot wallets, governance and upgrade multisigs, then validator keys.
Each category has a different migration timeline and political weight. Together, they describe a live financial system that must upgrade itself while running at full capacity, with hundreds of millions of accounts and no acceptable flag day.
Account abstraction is EF’s primary execution-layer migration path because it allows users to replace ECDSA-based authentication without forcing a chain-wide reset.
EIP-4337 infrastructure already supports more than 26 million smart wallets and 170 million UserOperations, which is still a fraction of Ethereum’s active user surface.
DefiLlama currently shows roughly 680,777 active Ethereum addresses, with 206,823 new addresses in the last 24 hours.
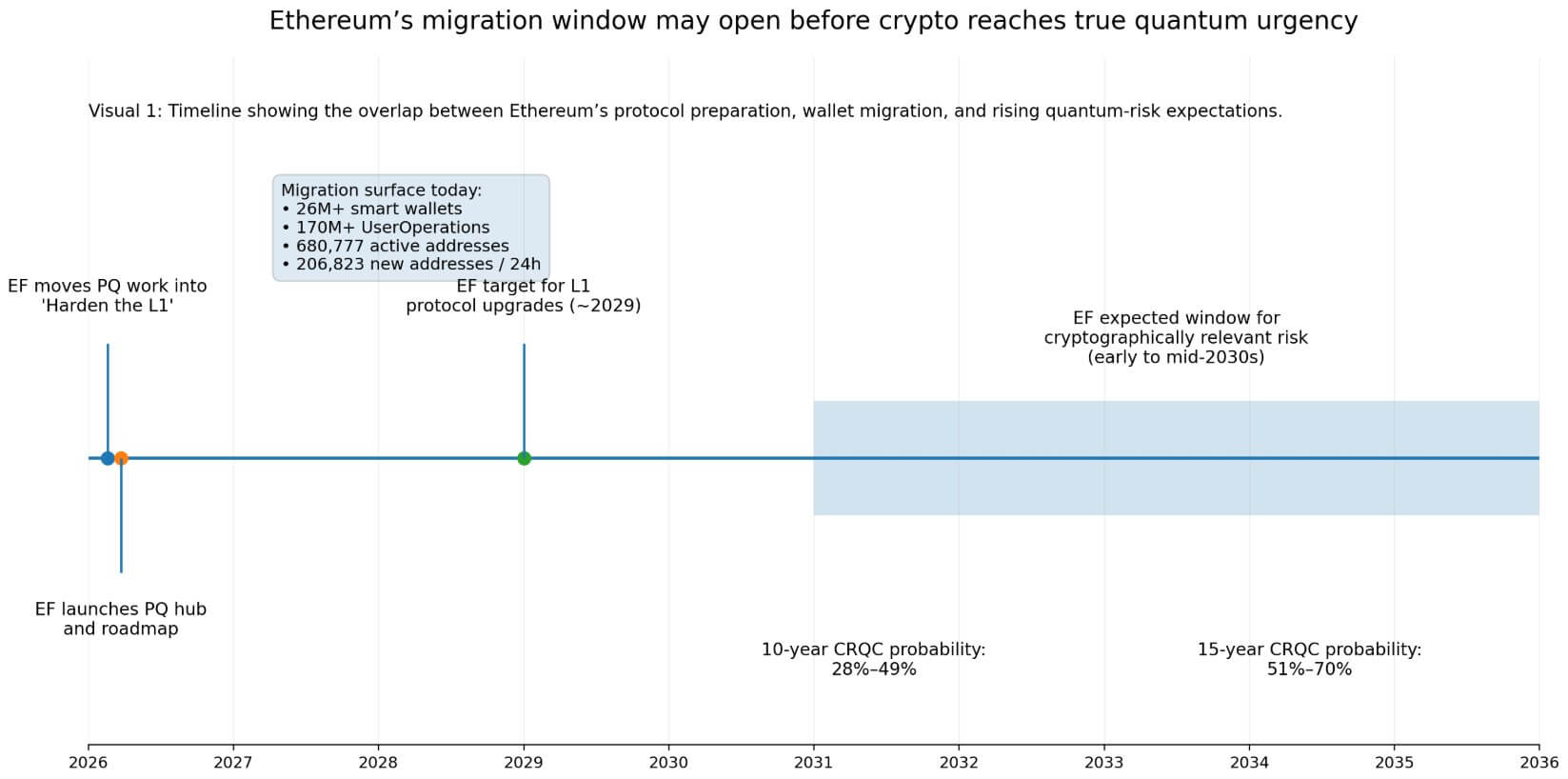
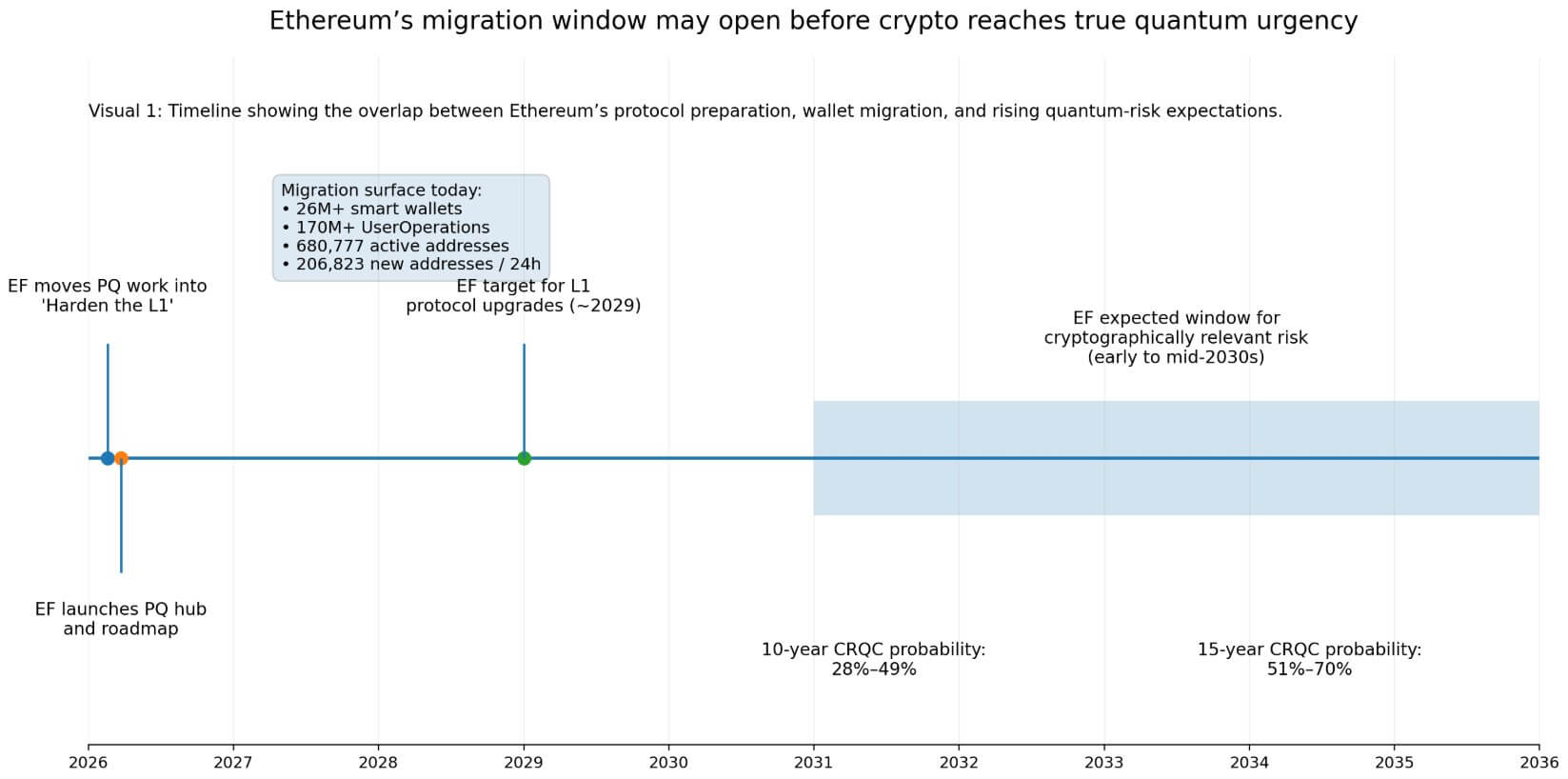
The Foundation’s timeline puts L1 protocol upgrades at roughly 2029, with full execution-layer migration taking additional years beyond that. EF says that most expert roadmaps place cryptographic relevance in the early to mid-2030s.
The Global Risk Institute’s 2025 quantum-threat survey puts the probability of a cryptographically relevant quantum computer emerging within 10 years at 28%-49% and within 15 years at 51%-70%, with respondents noting that the timeline has accelerated.
That overlap between L1 preparation and user-wallet migration is where the operational exposure actually lives.
However, that timeline looks tighter this week. Google’s new warning compresses the policy and market timetable even if the science remains uncertain. Google is now planning against a 2029 Q-Day horizon. While this does not settle when a cryptographically relevant quantum computer will arrive, it does change the operational framing.
Once major infrastructure operators start budgeting and planning for a shorter window, post-quantum readiness stops being a distant research topic and becomes a near-cycle execution problem for wallets, bridges, custodians, and validators.
Where capital and control concentrate
The bridge and custody layer sharpens that exposure considerably.
L2Beat shows Ethereum-linked L2s securing about $32.54 billion in value, while DefiLlama shows bridge protocols on Ethereum holding roughly $7.275 billion in total value locked, with bridge rails processing about $18.835 billion in volume over the last month.
Those flows run through a relatively compact set of key-management choke points, which are exactly the “high-value operational keys” EF places second in its risk hierarchy.
TRM Labs’ January 2026 crime report found that infrastructure attacks on keys, wallets, and access-control systems drove the majority of crypto’s $2.87 billion in 2025 hack losses, outpacing smart contract exploits.
The operational discipline the post-quantum roadmap requires in this domain mirrors the discipline the industry is already failing at today, which makes bridge and custody key rotation urgent on two timelines simultaneously.
The validator layer adds a different dimension to the coordination problem.
Beaconcha.in shows roughly 976,204 active validators and 36.67 million ETH staked, which looks like a maximally decentralized key-migration problem at first glance.
At the entity level, Lido holds 21.24% of the net staking share, Binance 8.73%, Ether.fi 6.05%, and Coinbase 4.64%, with those four operators controlling roughly 40.66% combined.
Validator key rotation is simultaneously a mass-coordination problem and a concentrated-operator problem.
| Surface | Key stat | Why it matters | Type of risk | Migration challenge |
|---|---|---|---|---|
| User accounts / EOAs | 680,777 active addresses; 206,823 new / 24h | Largest live surface | Theft / impersonation | User-by-user migration |
| Smart-wallet rails | 26M+ smart wallets; 170M+ UserOps | Existing migration path | Uneven adoption | UX + wallet tooling |
| Bridges | $7.275B TVL; $18.835B monthly volume | Value concentrated in few key sets | Operational key compromise | Fast institutional rotation needed |
| Ethereum-linked L2s | $32.54B value secured | Large capital stack depends on infra | Indirect ecosystem spillover | Cross-system coordination |
| Validators | 976,204 active; 36.67M ETH staked | Huge validator set | Network operations risk | Mass + concentrated operator migration |
| Top staking entities | Lido 21.24%, Binance 8.73%, Ether.fi 6.05%, Coinbase 4.64% | Top four control 40.66% combined | Operator concentration | Early movers set the pace |
If major staking platforms rotate keys early, migration momentum builds naturally, and the smaller validator cohort follows clear precedents. If large operators drag, the compliance burden falls disproportionately on independent validators, who lack the operational infrastructure to bear it alone.
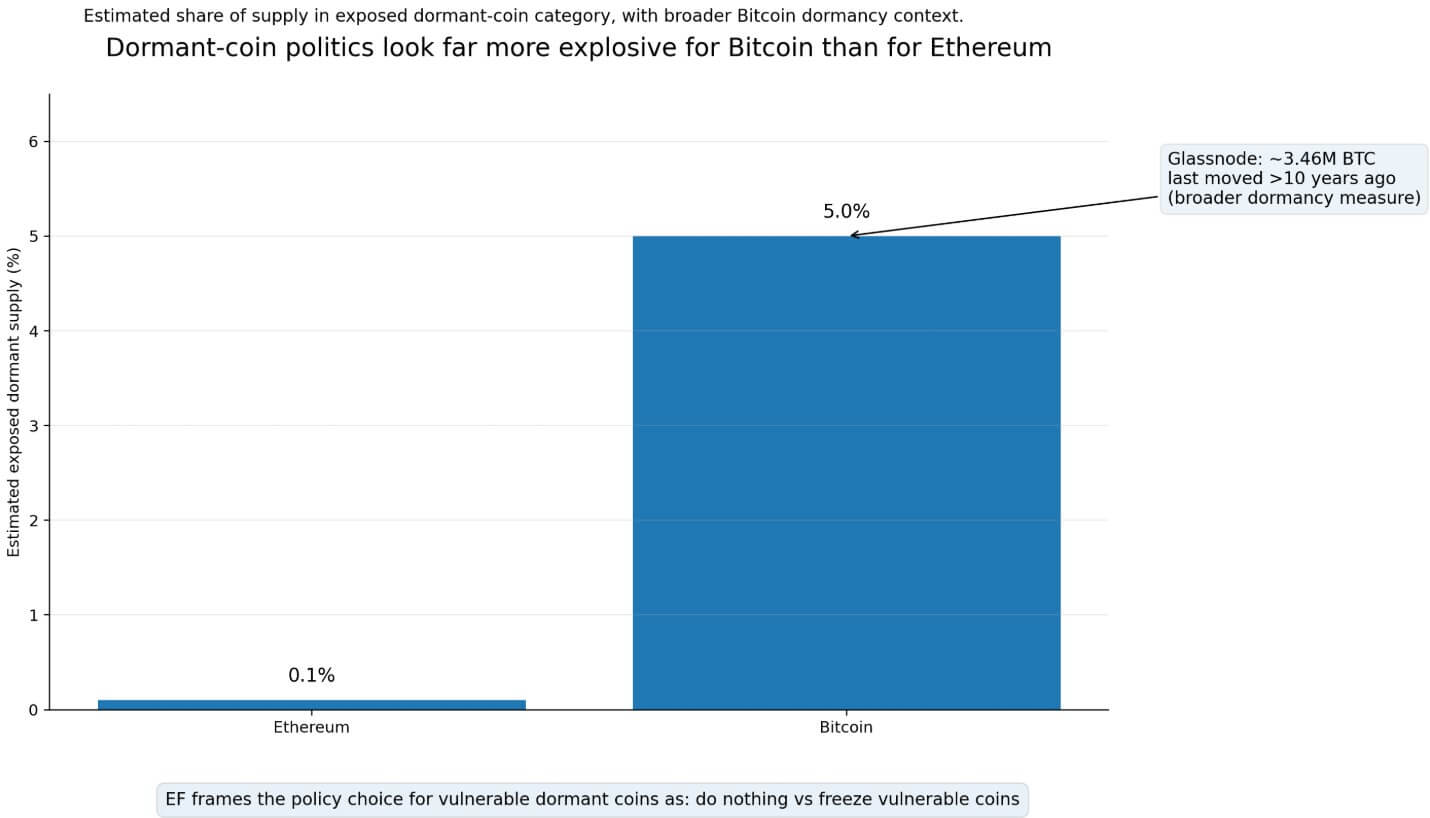
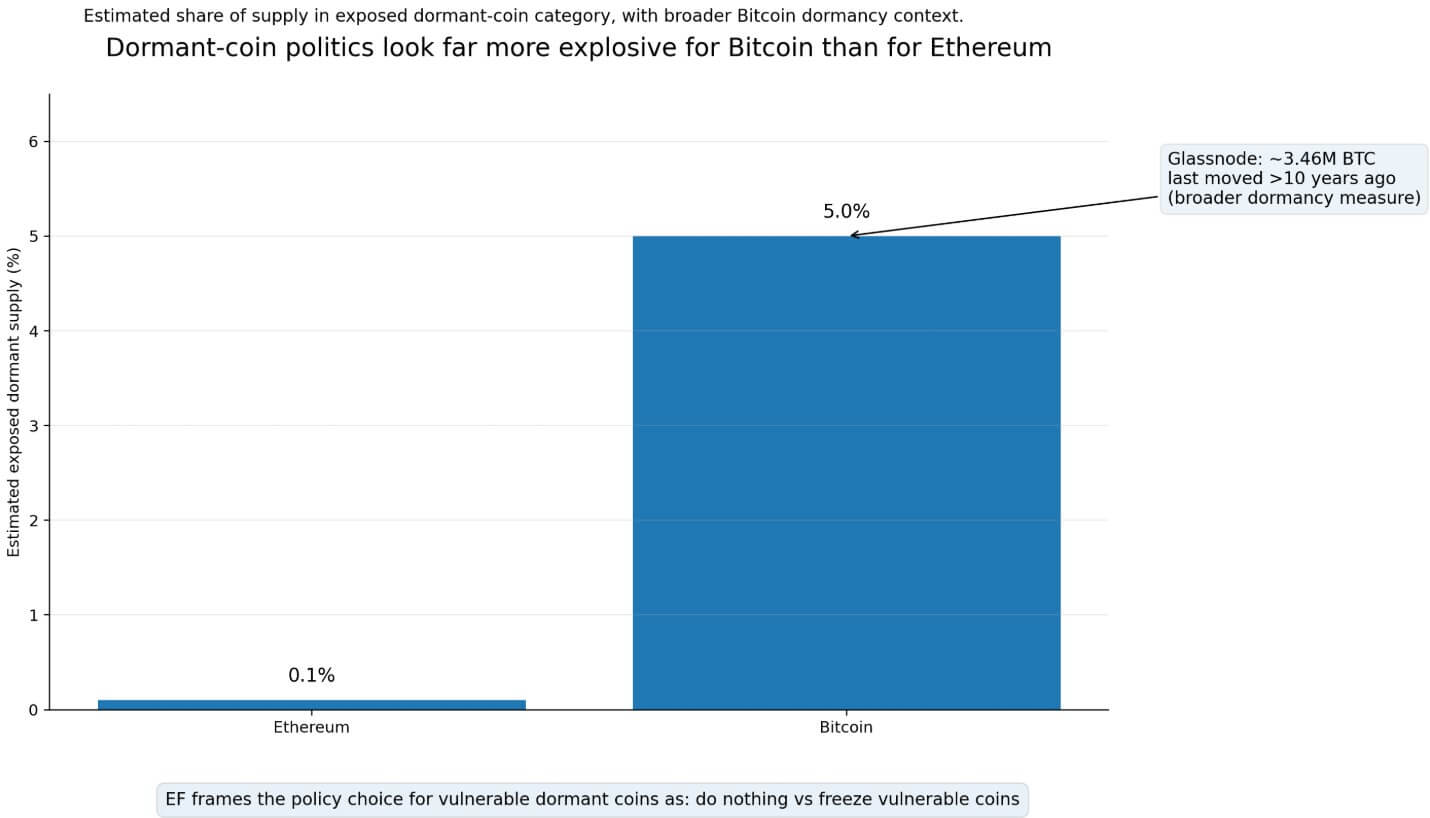
EF frames the dormant coin case as the most politically charged element of the roadmap.
Accounts that have never revealed a public key have no direct quantum exposure, as their key remains hidden within an address.
Accounts that transacted, exposed their public keys, and then went silent are a different category entirely, leaving funds vulnerable with no mechanism for self-migration.
EF’s FAQ names two natural outcomes when the risk window arrives: do nothing, or freeze vulnerable coins. EF explicitly frames that choice as a community governance decision, one requiring social consensus on who gets protected and under what conditions.
EF estimates Ethereum’s exposure in this category at roughly 0.1% of supply, and Bitcoin’s runs closer to 5%, tied to early address formats that many consider abandoned.
a16z’s Justin Thaler has argued Bitcoin is uniquely exposed because early P2PK outputs put public keys directly on-chain, and because Bitcoin’s governance structure makes coordinating any freeze politically severe.
Glassnode shows that about 3.46 million BTC have been inactive for more than 10 years, a broader dormancy measure that clarifies why any debate over dormant coins would be far more combustible on Bitcoin than on Ethereum.
Two outcomes
Ethereum rests on account abstraction infrastructure already running at scale.
If EIP-7702 and EIP-4337 tooling enable a large share of active users to migrate before quantum anxiety reaches a retail tipping point, Ethereum can absorb the transition without a governance crisis.
Bridges and custodians, controlling concentrated value and facing institutional due diligence demands, move first and establish migration norms across the industry.
With Ethereum’s low dormant exposure figures, “do nothing” remains politically viable, sparing the chain a contentious debate over a freeze.
In that scenario, Ethereum’s real advantage is upgrade agility: a live financial system that achieves quantum readiness through gradual, incentive-compatible migration, preserving continuity and user experience throughout.
However, if L1 milestones slip, execution-layer migration extends deeper into the 2030s, and the highest-value surfaces stay partly anchored to legacy assumptions as quantum timelines tighten. This is especially true if Google’s 2029 projection comes to fruition.
Because infrastructure attacks already account for most hacking losses today, markets are beginning to price operational lag as a security discount for custodians and bridge operators before any quantum computer becomes relevant.
Post-quantum readiness becomes a standard due diligence criterion for institutional allocators, and operators unable to demonstrate a credible migration timeline face capital outflows and escalating insurance costs.
The cryptographic threat causes reputational and capital costs to accumulate during the migration window itself, propelled by market perception of operational lag well ahead of any cryptographic event.
EF placed PQ work within the “Harden the L1” protocol track in February and explicitly tied native account abstraction to quantum readiness. The cryptography will advance on a predictable schedule.
The migration fight over wallets, bridges, and dormant coins is already underway.

















